Table of Contents >> Show >> Hide
- First: What “System Files” Means on Android
- Quick Map: Where You Can Go Without Root
- Method 1: Use the Built-In File Manager (And Enable Hidden Files)
- Method 2: Use a Computer (MTP) to Browse “Restricted” Folders
- Method 3: Use ADB to Access More (Safely) Without Root
- Method 4: Use Android Studio Device Explorer (No Root Required)
- Method 5: Shizuku + Wireless Debugging (Elevated Access Without Root)
- What You Still Can’t Do Without Root (And Why You Shouldn’t Try)
- Safety Rules Before You Touch Anything “System-ish”
- Real-World Experiences & Lessons (The Part Nobody Puts in the Quick Tips)
- Conclusion
Android is basically a very polite bouncer. It’ll happily let you into the lobby (your photos, downloads, and files),
but the moment you try to walk toward the VIP area (system folders, app data, protected directories), it crosses its arms
and says: “Nice try, buddy.”
The good news: you can access a lot more than most people realizeoften without rooting, without sketchy “one-click”
apps, and without turning your phone into a pocket-sized paperweight. The catch: “system files” means different things on
Android, and some doors are locked by design.
This guide breaks down what’s actually possible, what’s not, and the safest no-root methods that work in real life:
built-in file tools, a computer (MTP), ADB, Android Studio’s Device Explorer, and (when you need extra reach) Shizuku via
Wireless Debuggingwithout fully rooting your device.
First: What “System Files” Means on Android
People say “system files” when they mean one of these categories:
-
Shared storage files (easy): things under
/storage/emulated/0/like Downloads, DCIM,
Documents, Music, etc. -
App-specific external folders (sometimes tricky):
/storage/emulated/0/Android/data/and
/storage/emulated/0/Android/obb/heavily restricted on newer Android versions. -
App internal data (mostly locked):
/data/data/<package>/or
/data/user/0/<package>/protected by app sandboxing. -
System partitions (locked without root/unlocked system):
/system,/vendor,
/productread-only on modern devices and not meant for casual browsing.
Without rooting, you’ll mainly be working with the first twoand in limited, controlled ways, pieces of the third (usually
only for apps you develop or when an app exposes export/backup options).
Why Android Blocks You (And Why That’s a Good Thing)
Android’s security model is built around sandboxing: each app gets its own private space, and other apps (and you) aren’t
supposed to rummage around in it. Starting with Android 10 and especially Android 11+, Google tightened “scoped storage,”
meaning apps and file managers can’t freely crawl through everyone else’s folders anymore.
Translation: your phone isn’t “less powerful”it’s just less willing to let random apps treat your storage like an all-you-can-eat buffet.
Quick Map: Where You Can Go Without Root
Here’s the practical reality check:
- You can access: shared storage (
/storage/emulated/0/) with any file manager. -
You might access:
Android/dataandAndroid/obbusing built-in system file tools,
a computer (MTP), or Shizuku-based file managersdepending on Android version and OEM. -
You usually can’t access:
/data/datafor other apps (private app storage) without root. -
You can’t safely modify:
/systemor system partitions without root/unlocked modifications
(and even then, it’s risky).
If your goal is “I want to edit or copy files from Android system folders,” the safest approach is to
start with the least invasive method and only escalate if you truly need to.
Method 1: Use the Built-In File Manager (And Enable Hidden Files)
Most Android phones ship with at least one official file tool:
Google’s Files (often called “Files by Google”), an OEM file manager (like Samsung’s My Files),
and sometimes a “DocumentsUI” system picker behind the scenes.
Show Hidden Files
Hidden files are not automatically “system files,” but they’re often what people are searching forfolders that start with
a dot (.thumbnails, .cache) or media hidden by a .nomedia file.
- Open your file app.
- Find Settings.
- Toggle Show hidden files (wording varies).
If you’re trying to understand why photos/audio “disappear” in gallery apps, check for a .nomedia file inside
the folder. That tiny file basically hangs a “Do Not Index” sign for media scanners.
What This Method Is Best For
- Finding hidden cache folders eating storage space
- Inspecting app-created files in shared storage (downloads, exports, backups)
- Basic cleanup that doesn’t involve protected folders
Limitations
On Android 11+, your file app may refuse access to Android/data or let you browse but not modify.
That’s not you doing it wrongthat’s Android doing what it was designed to do.
Method 2: Use a Computer (MTP) to Browse “Restricted” Folders
Here’s the weird-but-true part: many devices that block on-device file managers from opening Android/data
will still allow access when connected to a computer via USB using MTP (Media Transfer Protocol).
How to Do It
- Connect your phone to a PC or Mac using a USB cable.
- On your phone, set USB mode to File transfer (MTP).
- Open the phone storage on your computer.
- Navigate to
Internal shared storage > Android > dataorobb.
If it works, you can copy files in/out like it’s 2014 again. If it doesn’t, your device/OEM may be stricteror you may
need a different method below.
Best Use Cases
- Backing up game files stored in
Android/obb(when allowed) - Recovering files when your on-device manager says “Access denied”
- Moving large folders faster than cloud syncing
Don’t Skip This Warning
Some apps store sensitive data under Android/data. Copying or modifying files can break apps, corrupt saves,
or violate an app’s terms. When in doubt, treat this as a backup and restore operationnot a playground.
Method 3: Use ADB to Access More (Safely) Without Root
ADB (Android Debug Bridge) is the official command-line tool for communicating with Android devices. It’s not inherently “hacky.”
Developers use it every day for debugging, file transfer, and device inspection.
What ADB Can Do Without Root
- Pull/push files in shared storage (
/sdcard//storage/emulated/0) - Open a shell and inspect many non-protected directories
- Access your own app’s data via
run-asif the app is debuggable - Pair with Wireless Debugging on newer Android versions (no cable needed after setup)
Setup (High Level)
- Enable Developer options (tap Build number several times).
- Enable USB debugging.
- Install Android Platform Tools (ADB) on your computer.
- Connect your phone and approve the debugging prompt.
Useful ADB Commands
1) Verify the device is connected
2) Start a shell session
3) List shared storage
4) Copy files from phone to computer
5) Copy files from computer to phone
About Those “Permission Denied” Errors
If you try something like:
…you’ll almost certainly get blocked on a non-rooted phone. That’s normal: the ADB shell user is not allowed to read other apps’ private directories.
The run-as Trick (Only for Debuggable Apps)
If you’re a developer (or you’re testing an app that was built as debuggable), you can access that app’s private storage:
This is extremely useful for grabbing your own app’s databases, preferences, or internal fileswithout rooting.
For regular Play Store apps, run-as usually won’t work because most production apps are not debuggable.
Method 4: Use Android Studio Device Explorer (No Root Required)
If you’d rather click than type, Android Studio includes Device Explorer (formerly Device File Explorer),
which can browse device files, copy them, and inspect app storagewithin the permissions allowed.
Why It’s Worth Using
- Easy browsing of shared storage and app-related directories
- Great for developers testing file output and debugging storage issues
- Less error-prone than manual shell commands when you’re in a hurry
Reality Check
Device Explorer will not magically unlock other apps’ private data on a non-rooted device. If you can’t access it with ADB permissions,
Device Explorer won’t either. But for your own app testing and general storage inspection, it’s one of the cleanest tools available.
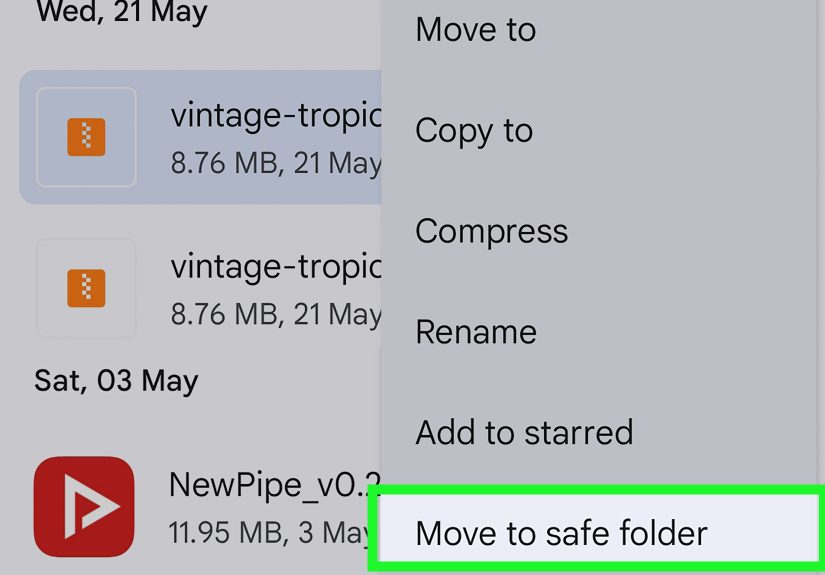
Method 5: Shizuku + Wireless Debugging (Elevated Access Without Root)
If you’ve been battling the “Access denied” wall for Android/data and Android/obb,
you’ve probably heard the name Shizuku.
In plain English: Shizuku can let certain apps call system APIs with ADB-level privileges. On Android 11+,
it can be started using Wireless Debugging (no permanent root required). Then compatible file managers can sometimes
manage folders that are otherwise blocked to normal apps.
When This Makes Sense
- You need to access
Android/data/Android/obbon-device and MTP isn’t an option - You want a reversible setup (turn it off when you’re done)
- You understand that this is still “power-user mode” and should be treated carefully
What to Watch Out For
- Some OEMs restrict ADB permissions more aggressively than others.
- Android version updates can break workarounds that used to work.
- You are expanding what apps can doso only use trusted apps and disable when finished.
If this method feels like borrowing the janitor’s master key for “just five minutes,” that’s a fair analogy.
It’s not the same as rootingbut it’s also not “normal mode.”
What You Still Can’t Do Without Root (And Why You Shouldn’t Try)
Some tasks are intentionally out of reach without rooting or heavy device modification:
-
Reading other apps’ private data in
/data/data(databases, tokens, internal settings). -
Editing system partitions like
/systemon production devices (they’re typically read-only and protected). - Bypassing Android security models using shady “root-free” miracle tools (the miracle is usually malware).
If your goal is troubleshooting (not snooping), there’s usually a safer alternative:
export data from the app, use built-in backup features, or use developer tools for apps you control.
Safety Rules Before You Touch Anything “System-ish”
- Backup first. Copy folders out before deleting or editing.
- Prefer read-only actions. Viewing and copying is safer than modifying.
- Don’t delete random folders to “free space.” Cache folders can be safe to clear; system folders are not.
- Watch for app integrity checks. Games and secure apps may break if files are altered.
- Disable debugging when you’re done. Especially Wireless Debugging and USB debugging.
Real-World Experiences & Lessons (The Part Nobody Puts in the Quick Tips)
Here’s what typically happens when people go hunting for Android system files without rootbased on common, repeatable scenarios
you’ll see across forums, dev docs, and (occasionally) frantic group chats that start with “uh… my phone is acting weird.”
1) The “Android/data” Folder Is a Moving Target
The first surprise is how inconsistent Android/data feels. One phone lets a file manager browse it. Another blocks everything.
A third lets you open it only through a system picker. Then you update Android (or the OEM updates the file app),
and the exact same steps suddenly stop working.
The lesson: treat access methods like layers. If on-device access fails, try MTP on a computer. If MTP fails,
consider ADB or Shizuku. And if you’re doing something mission-critical (like backing up a project folder or a game save),
don’t wait until your phone updates overnight and locks the doormake a backup now.
2) “Permission Denied” Usually Means “Wrong Door,” Not “Game Over”
People often interpret a permission error as “I can’t do this at all.” Sometimes that’s true (like other apps’ private
data under /data/data), but often it’s just the wrong access path.
Example: if you try to reach an app’s internal database directly with ADB on a production app, Android blocks you.
But that doesn’t mean you’re stuckyou may be able to:
- export from the app (many apps have “Export” or “Backup”)
- use official developer tooling (Device Explorer) for apps you develop
- retrieve files that are intentionally stored in shared storage (Downloads/Documents)
The mindset shift: ask “where does the app legitimately expose data?” instead of “how do I pry open the private vault?”
3) The Best File Manager Is Sometimes… the Stock One
It’s counterintuitive, but newer Android restrictions often mean third-party file apps are at a disadvantage.
Sometimes the only tool that can navigate certain corners is a built-in system file interface (or the OEM’s file manager),
because it has privileges third-party apps don’t get.
So if your favorite file manager can’t open a folder, don’t assume it’s “bad.” It might simply be playing by Android’s rules.
Try the stock Files app, the OEM file tool, a computer connection, or an official system picker workflow.
4) ADB Feels Scary Until It Saves You
Many people avoid ADB because it looks like “developer stuff.” But for basic file access and backups, it’s often the cleanest,
most predictable option. It doesn’t rely on a file manager’s UI quirks, and it tends to behave consistently across devices.
The trick is to keep your ADB usage boring: list directories, pull files, push filesavoid random commands you found in a comment thread
at 2 a.m. If you can explain what a command does in one sentence, you’re probably safe. If it’s a 40-line script that promises to “unlock everything,”
that’s how people end up factory resetting on a Tuesday.
5) “No Root” Still Requires Responsible Choices
Even without rooting, methods like Wireless Debugging + Shizuku can widen what apps can do. That’s powerfuland it means you should be picky
about which apps you trust with elevated permissions. A good habit is to enable the setup, do the task, then disable it.
Think of it like using a hotel room safe: you don’t leave it open forever just because you can.
Bottom line: the safest path is not “one magical trick.” It’s having a small toolkit and using the least invasive option that gets the job done.
Conclusion
Accessing Android system files without rooting is absolutely possiblejust not in the Hollywood “hack the mainframe” way.
Most of what you want lives in shared storage, and for the tricky areas (like Android/data), you can often rely on
a computer connection, official ADB tools, or carefully managed elevated-access helpers.
If you remember one rule, make it this: copy first, edit later. Android’s protections aren’t there to annoy you
they’re there to keep your device stable, secure, and less likely to become a very expensive pocket warmer.